Information barriers have always been a challenge for organisations to manage, monitor and control. As a result, many firms have historically banned home working and previously only enabled access to files, folders, and other information on-site. Along comes the Covid-19 pandemic, and suddenly all rules needed to be re-administered to facilitate the new remote working conditions – forcing firms to completely rethink how they manage the exchange of confidential information between employees.
What are information barriers?
‘Information Barriers’, ‘Ethical Walls’ or ‘Chinese Walls’ refer to the ethical separation between departments or individuals to block the exchange of confidential information. The term Chinese wall appeared during the 1930s after the stock market crash of 1929, requiring segregation within investment banking departments.
In line with the increasing number of capital transfers, the practice of information barriers has been expanded over recent decades to protect investors, clients, and other key stakeholders from the leakage of confidential information. There are several ways in which firms can do this and includes things like physically separating departments, monitoring conversations between employees and clients, splitting up record keeping systems, and setting up access controls. Whilst all financial firms had policies to this effect prior to lockdown, managing and monitoring information barriers became nearly impossible when the standard practice of restricting the physical location of people and flow of information in a controlled office environment was forced to change overnight.
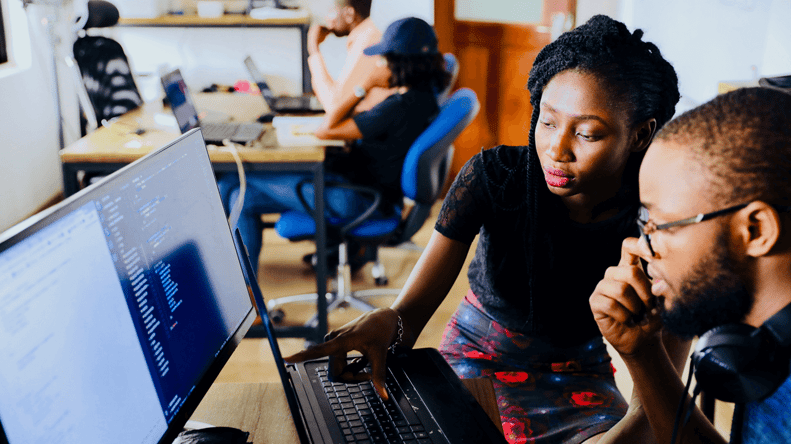
Difficulties managing information barriers with a remote workforce
In an office environment, physical rooms, and the movement of people between them can be easily monitored and restricted. This is not possible when employees are working remotely. It is also harder for compliance teams to control the spread of confidential information once it has left the office. Documents are suddenly signed, sealed, and delivered electronically, with a much higher risk of confidential information being inadvertently shared by roommates, family members or friends.
When lockdown set in and employees started working outside of the control office environment, the use of e-communication platforms and devices skyrocketed, increasing the number of channels that confidential information could be shared on. Conversations that previously would be carried out in person, suddenly all took place electronically. And while these should all be captured and recorded on approved and recordable corporate communications channels, it is extremely difficult for organisations to control how and where employees communicate and share content in a remote working environment
In fact, according to a recent The Wall Street Journal article “employers worry that workers may be more likely to ignore rules or take shortcuts when they work from home, and lose touch with some reminders of corporate policies”.
As a result, the risks associated with maintaining information barriers in financial services have significantly increased, requiring most firms to completely rewrite their policies. And whilst many firms believe that the gradual return to the office will lessen the blow, the risk will remain until people are back in the office full time, or new rules can be adhered to.
How can compliance officers monitor and control information barriers in a remote working environment?
Traditionally, these functions have been heavily dependent on manual processes. And whilst there is high long-term cost and risk associated with this legacy set-up, many organisations continue to rely on it. The risks include human error, not being able to adapt to changing conditions quickly enough, and of course financial implications. Falling short of safeguarding information can ultimately lead to conflicts of interest and loss of income.
To ensure the successful implementation of information barriers, compliance officers need to follow actions beyond just the physical separation of the departments. This includes:
-
Defining an information policy which covers on-site and remote working, and ensuring that everyone has an in-depth understanding of what it entails
According to a recent IBM survey, 45% of people working remotely supported that their firms provided no appropriate training on securing devices at home. Compliance teams need to understand and educate individuals on what the information policy looks like, how it adapts depending on the location of employees, and how it can monitor for breaches in either scenario. Of course, this is much easier if everything and everyone is in one place and is complicated in remote working conditions.
-
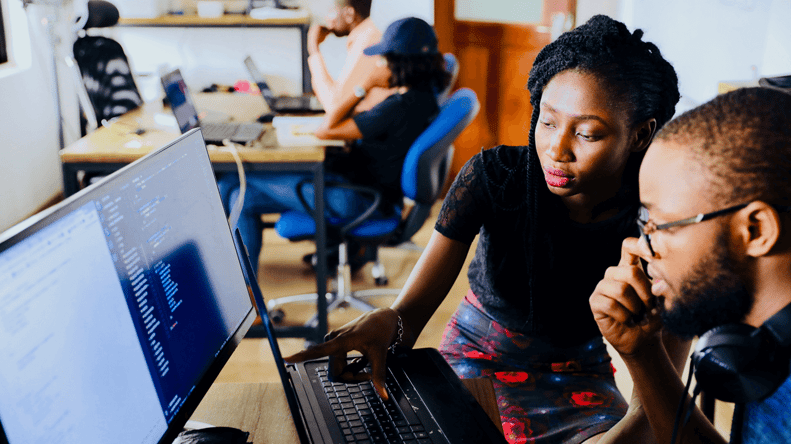
Monitoring interactions between segregated groups without having to manually review communications
Reading all emails and listening to all voice calls is just not a feasible assumption. Firms need to deploy technologies that can actively transcribe, analyse, and monitor communications – flagging any suspicious behaviours or activities that meet specific criteria. The role of surveillance needs to move away from reactive monitoring to proactive rule creation, where risks are identified, managed, and mitigated before information breaches, misconduct, market abuse or other risks have occurred.
-
Overlaying both structured and unstructured data
There are significant advantages in using a single platform to overlay structured data (such as transaction or order details) alongside unstructured data (such as communications). When this information is overlaid on a single platform, compliance teams can gain additional insight to detect siloed and combined breaches of market abuse, information barriers and other risks. A data-centric approach to compliance enables truly holistic oversight and proactive identification of risks. Regulated firms are already capturing transaction details, documents, communications, meeting minutes and more as part of their record keeping obligations. Integrating these pieces of information into a system that uses rules and policies to actively monitor across all the data sets, helps to reduce the risk of missing key breeches set around ethical communication walls. With all the information in one place, it becomes easier for firms to apply sensitivity labels to classify confidential data and set up customised alerts based on the access.
-
Actively monitoring for breaches
Your policies surrounding active communication monitoring and information sharing should also include relevant workflow and case management tools. Who should be alerted? How will you act on the details? How proactively should you use the information collected to enhance future rules and policies? These are all questions that you should be considering on an ongoing basis.
Looking ahead - The future of managing information barriers in financial servises
As the ability to work remotely becomes accepted across the industry, digital communications will increase. Compliance officers cannot prohibit information sharing in its entirety but need to use efficient systems that enable employees to share information according to the organisation’s policy.
Whilst there is a plethora of intelligent and highly automated solutions available in the market today that enable effortless compliance, many organisations continue to rely on legacy technology. A common objection to upgrading processes or deploying new systems is the initial capital outlay and effort required. However, as regulators across the world continue to work together to ensure markets preserve the highest standards of integrity, perhaps this no longer is an option? Lockdown hopefully has made it clear to organisations that they need to prioritise their compliance processes, focus on their data, and modernise their technology.
Related READING:

COMPLIANCE IN ISOLATION PART 1: PLAYING BY THE RULES
How seriously should you be taking your compliance obligations during this lockdown period? Arguably it is now more important than ever!
COMPLIANCE IN ISOLATION PART 2: YOUR CHECKLIST FOR REMOTE WORKING
10 things Risk and Compliance Officers should be thinking about now that most companies are firmly on lockdown and supporting a remote workforce.