Last week, we had the pleasure of attending a thought-provoking and topical lunch-and-learn at the SIFMA Compliance and Legal Seminar in San Diego. While the conference as a whole was filled with impactful sessions, we walked away from this particular discussion with an increased appetite to weigh in on the industry-wide issue around unmonitored & unauthorized communication channels, which we have shared below.
The ABC of Unmonitored & Unauthorized Communication Channels:
Hosted and moderated by QuisLex, the session offered strong insights into the challenges firms face in dealing with the proliferation of channels used for communications relating to “business as such.” The phrase “business as such” is of importance because it is the term used in the rules and guidance published by FINRA and is taken directly from the Reporting Requirements for Brokers or Dealers under the Securities Exchange Act of 1934, SEC Release No. 34-38245.
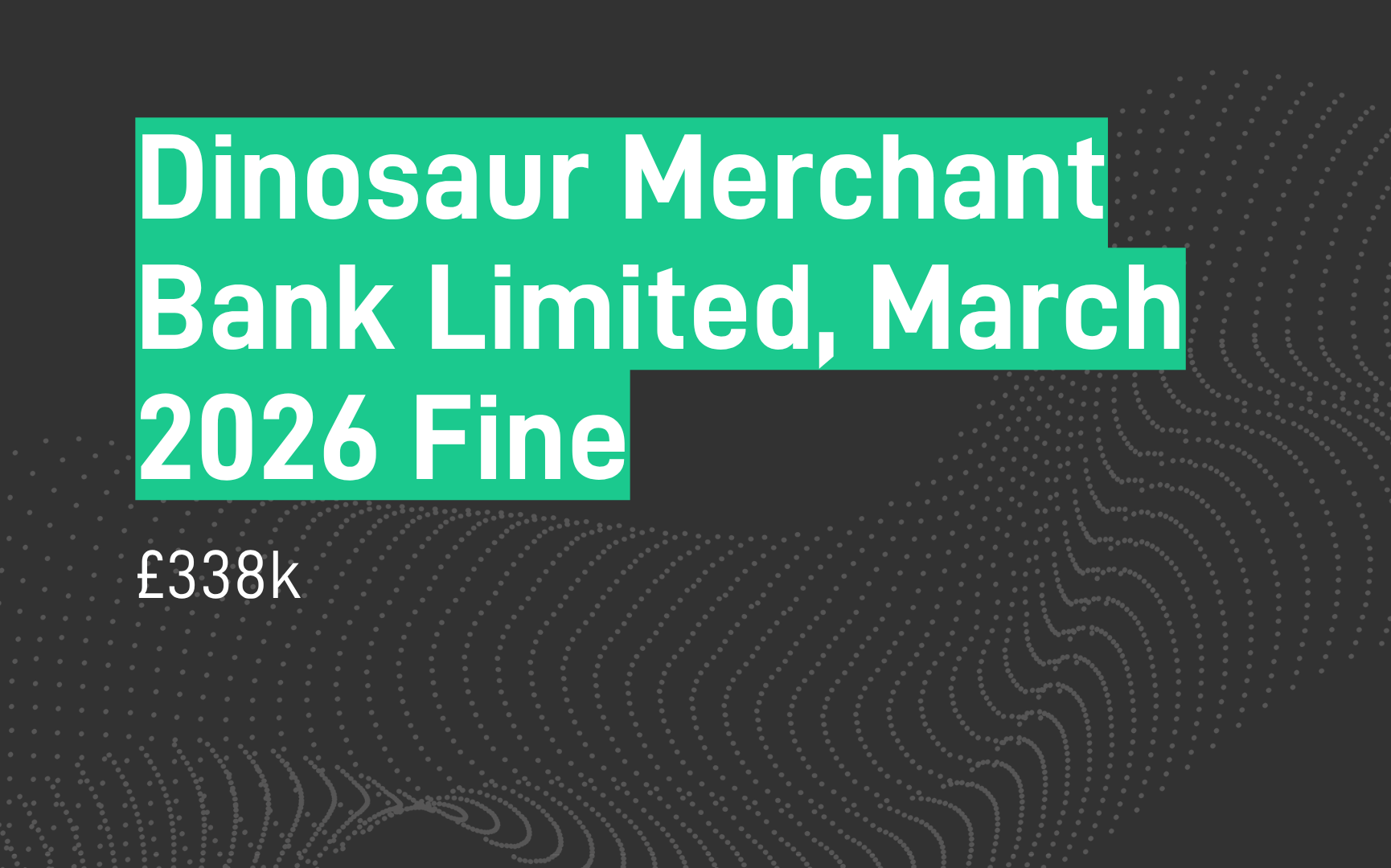
Everyone in the financial services landscape is well aware of the nearly $2bn in fines handed out by the SEC and CFTC in 2022 for “widespread and longstanding failures by the firms and their employees to maintain and preserve electronic communications.” Those fines have caused financial firms doing business in the US to take a hard look at how they deal with the various messaging apps that have become commonplace in our personal lives and have crept into “business as such” communications to varying degrees.

What intrigues us is the breadth and energy of the conversation that continues to take place. As a software solutions provider in compliance, we have the technology to solve “the problem.” SteelEye can ingest, archive, surveil, and report on over 85 communications channels, including WhatsApp, SMS, Signal, Telegram, and iOS, to name a few. So why isn’t it case closed? Why isn’t the phone simply ringing off the hook? Why do we even need to come to these conferences anymore?
It turns out, as is often the case, that the problem is a bit more nuanced. Firstly, the session that so ably discussed and debated the challenge didn’t include technologists and was instead comprised of lawyers and compliance specialists. Celia Cohen (Partner, Ballard Spahr LLP), Brian Corbin (VP, Legal Solutions and Operational Excellence, QuisLex), and Therese Craparo (Partner, Reed Smith LLP) made up the panel. As a result, very little of the discussion, as well as the questions posed by the audience, was committed to technology, which made it difficult for us to work my gratuitous plug into the narrative.
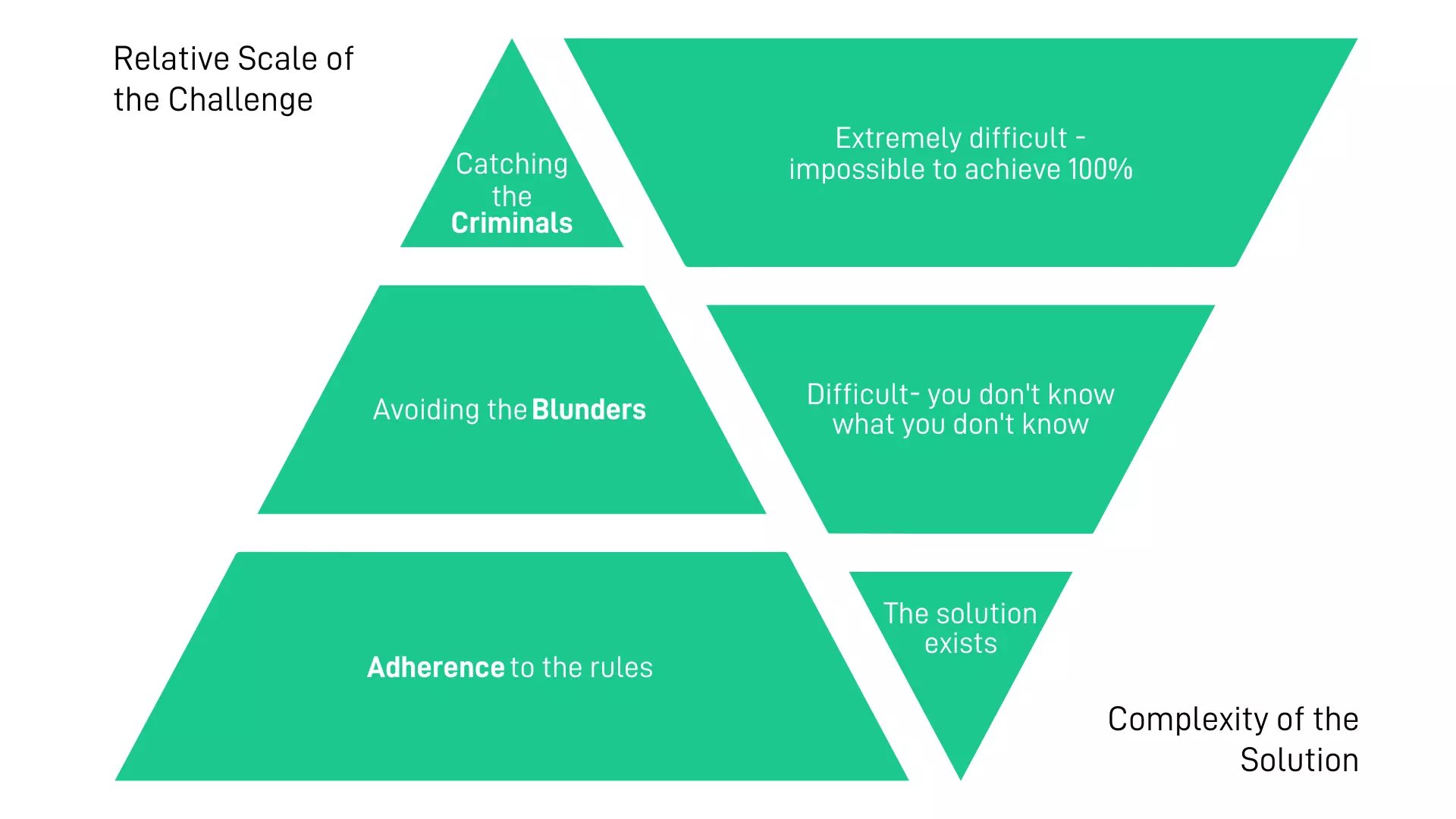
That said, we did learn a great deal and we walked away with some key insights to help SteelEye in positioning our solutions, as well as help the folks responsible for implementation at regulated firms. Our main takeaway from the event is that the problem should be considered in three distinct layers, which we cunningly turned into an A. B. C. framework: Adherence, Blunders, and Criminality.
Layer 1: Adherence
This is the core problem, as firms simply haven’t been adhering to the rules. SEC Release No. 34-38245 does not include or exclude messaging apps, text messages, etc. The rule simply says, "the supervisory requirements for electronic communications should be based on the content and audience of the message and not merely the electronic form of the communication." Thus, if the content and audience imply “business as such,” then the communication must be recorded. This means that not every text between a broker and a customer is required to be included. A quick text confirming a 'tee time' at a charity golf event would likely not be considered “business as such,” but the exchange found below would, including the use of emojis.
The tier-one banks that were penalized in the SEC and CFTC messaging probe weren’t fined for nefarious behavior, or anything related to collusion or inappropriate sharing of information. They simply weren’t adhering to their regulatory obligations. The good news is that most people in any given organization are law-abiding and motivated to do the right thing. Provided the tools, policies, and procedures are in place, they will be adhered to. We’ll talk about the solutions to increase adherence in the next installment of this blog.
Layer 2: Blunders
B is for blunders - mistakes, inaccuracies, and gaffes. Even with the best of intentions, mistakes will be made, gaps will be found, and compliance obligations will not be met. Regulators understand this and will generally not fine firms for their initial blunders, provided they see a plan for improvement, followed by an action.
A substantial portion of the panel discussion focused on the ongoing maintenance of programs, testing the process, and proving the controls. When it comes to unmonitored communications, a common problem is the embedding of communication apps and messaging tools into other software solutions, both bought and built. This trend means that new business approval committees need to be aware of the impact of communications on the compliance program. The fines have certainly heightened that awareness and folks who haven’t been caught up in the web yet can consider themselves lucky that they are able to learn from others’ mistakes.
Layer 3: Criminality
Conmen, cads, corruption, collusion, circumvention – there is no shortage of “C” words when describing the people and behaviors that tend to get the most airtime. Yet, they represent the thinnest layer in the challenge cake. Firms must create policies and provide tools that allow for the majority to abide by the rules, as well as offer the training, controls, and guidance to steer clear of avoidable missteps. However, once this has been done, it’s time to deal with an unfortunate reality - there will always be those intent on undermining the process and side-stepping the rules.
Given how few people, relatively speaking, proactively seek to undermine the process and consciously breach compliance, we were surprised at how much of the discussion last week focused on this end of the challenge spectrum. At one point, we felt the conversation was conflating the difficulty of detection of malfeasance with the sanctions handed out by regulators. This was at odds with the opinion we expressed earlier, that the problem and the reason for the huge fines, was a lack of basic adherence and respect for the rules, not the failure to identify a couple of rogue individuals leveraging unauthorized communications to share MNPI (material non-public information). The fines would have been less broad and less punitive at an industry level if the problem was that a collective of robust compliance programs had failed to detect those bad actors. That said, we do understand where the enthusiasm for this component of the problem stems from, as these are typically the press-grabbing and reputationally destructive headlines that people outside the industry pay attention to.
The Comms Problem: Perception vs Reality
We believe the old adage is true - a picture is worth a thousand words, and the issue at hand can best be conveyed through the graphic below, which compares the relative scale of the challenge to the complexity of the solution.
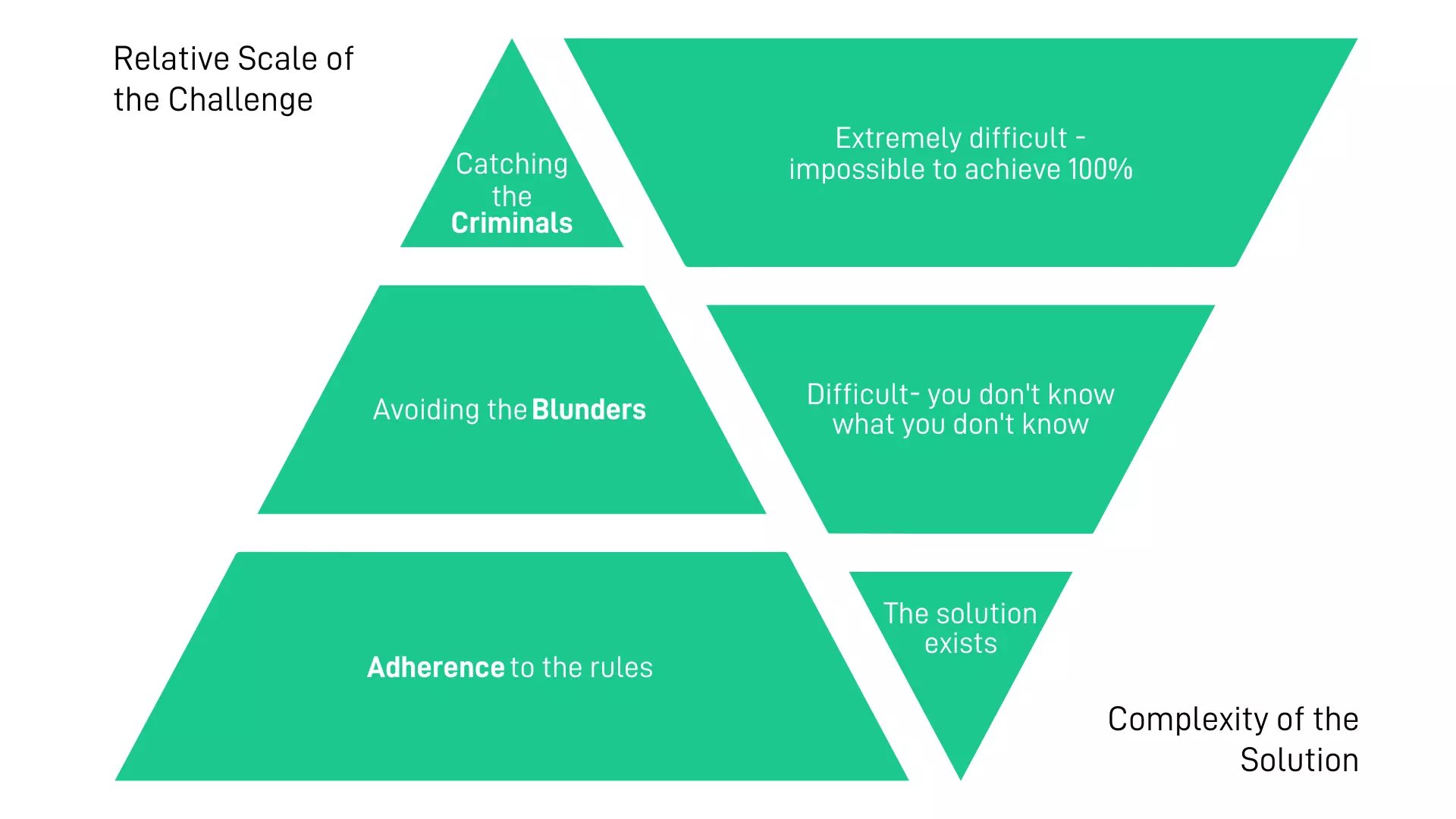
In short, the layer that represents the core challenge for financial firms (adherence) is, in fact, the most solvable, while the criminality piece only makes up a small portion of those violations, yet is far from an easy fix.
In the next installment of this blog, we’ll discuss the solutions to all three layers of the challenge, including how the use of an integrated surveillance system like SteelEye’s can greatly reduce the headaches for firms looking to remain compliant when it comes to their communications channels.
Lastly, we’d like to thank the SIFMA Compliance and Legal Seminar for providing its attendees with three days of insightful sessions and stimulating conversations, including this specific lunch-and-learn panel. The road to compliance is an ongoing journey rather than an end destination, and we look forward to returning next year to continue to build the roadmap for financial firms.
To see our platform in action, or to learn more about how we can help your firm gain a competitive advantage, contact our team of compliance experts now.
Turn Supervision into Super Vision
SPEAK WITH US TODAY